The following series of web page images shows the iSecMap security enforcement tool. After installing the iSecMap, a baseline of security information is mapped on your system and stored. At any time after installation, you can check to see what security information has changed. The main product menu looks like this:
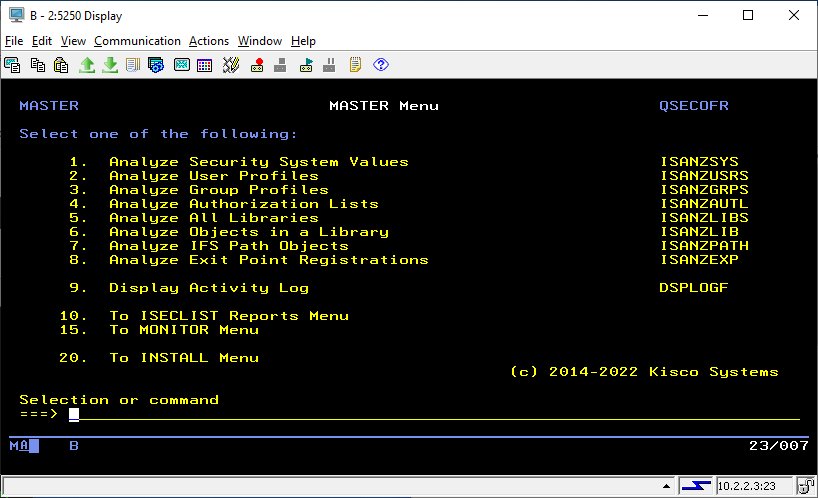
From this menu, you can check on any of the mapped security information using the different menu options.
For example, you can select menu option #1 to see if any of the security system values on your system have been changed since the baseline was last mapped. If a security change has been made, the display could look like this:
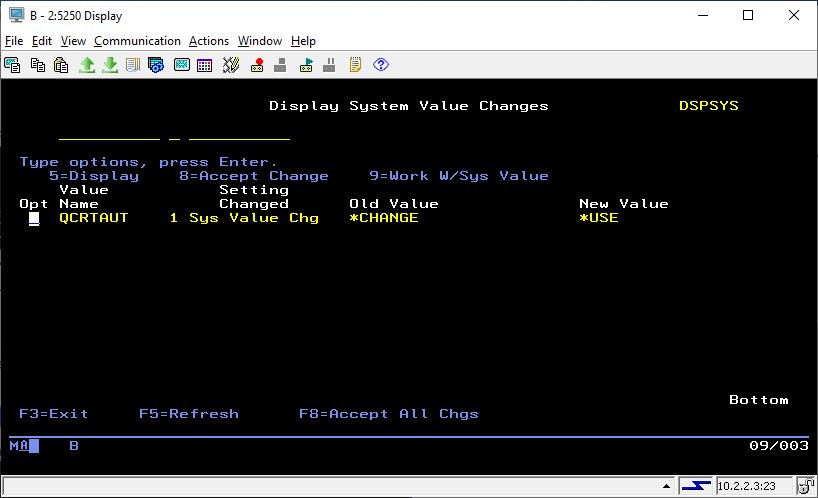
In this example, the system value QCRTAUT has been changed from *CHANGE to *USE. When you see this, you can either accept the new system value and make it part of a new baseline for security system values, or you can decide to work with the system value and change it back to where it was before the change.
You can repeat this same kind of exercise for the baseline information about user profiles, group profiles, authorization lists and library level security. You can also decide to track information about objects in libraries that you choose and objects in IFS paths that you choose. In each case, you can go back and periodically check the current security against your established baseline and work with changes.
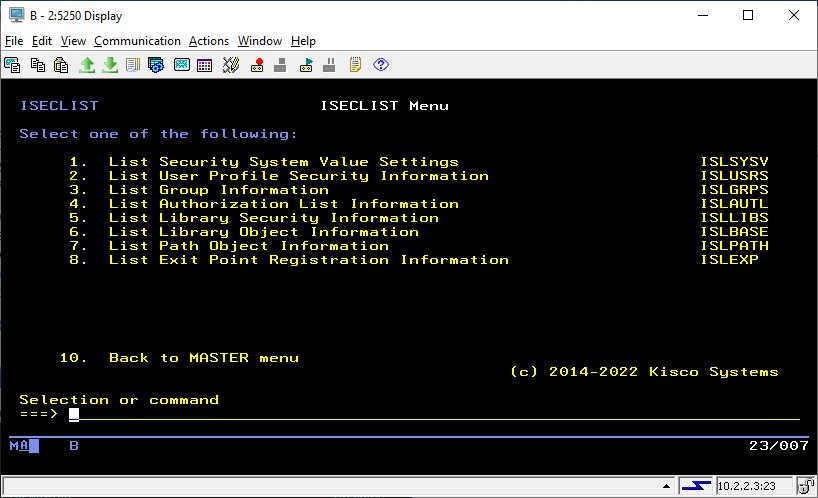
At any time, you can go to the reports menu and generate a listing of the current baseline information for any of the categories being tracked by iSecMap:
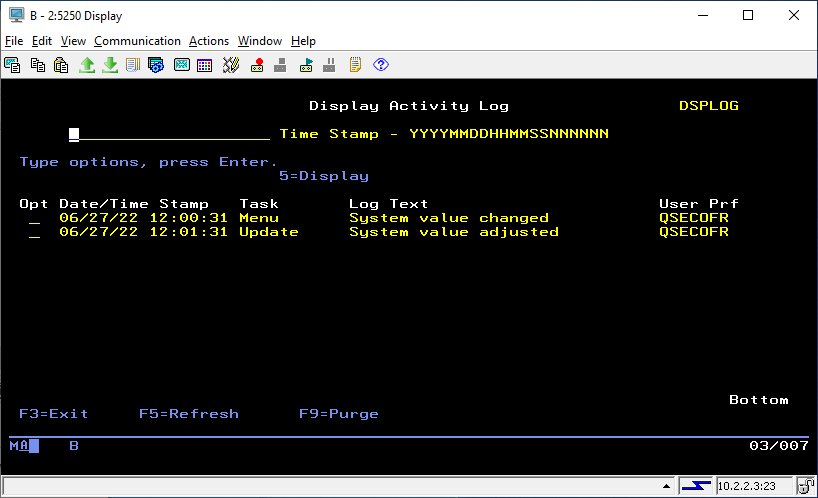
You can also use the iSecMap Security Monitor feature to have your system periodically check on the security environment automatically. You can specify how often you want the security checked and what level of check you want performed. Changes are reported live via messages and/or by email:
In this case, the system value change shown above was detected by the Security Monitor and reported by email notification.
All security activity within the scope of your configuration is automatically logged for reporting and audit purposes.